Wondering how to see someone else's Facebook messages without them knowing? Read this complete guide on dos and don'ts to view someone's Facebook messages.
Wondering how to see someone else's Facebook messages without them knowing? Read this complete guide on dos and don'ts to view someone's Facebook messages.
 There are many Hackers in this world who may be currently watching your activities daily and will try to snatch your personal information from you.
There are many Hackers in this world who may be currently watching your activities daily and will try to snatch your personal information from you.
 EC-Council’s Certified Ethical Hacker (CEH) is one of the most established and recognized offensive security certifications. The certification is ANSI-accredited and DoDD 8140-approved because of which the certification in highly valued by security professionals from both the public and private sectors. Since CEH is the gold standard for validating offensive security skills, the CEH certification cost is around $1,199 and the cost to retake the exam is $450. This article will cover the various processes you have to go through to earn this certification as well as the associated costs.
EC-Council’s Certified Ethical Hacker (CEH) is one of the most established and recognized offensive security certifications. The certification is ANSI-accredited and DoDD 8140-approved because of which the certification in highly valued by security professionals from both the public and private sectors. Since CEH is the gold standard for validating offensive security skills, the CEH certification cost is around $1,199 and the cost to retake the exam is $450. This article will cover the various processes you have to go through to earn this certification as well as the associated costs.
 Make an inexpensive BadUSB from an old USB drive and learn about Windows shortcut files and how malicious actors are using .lnk files to spread malware.
Make an inexpensive BadUSB from an old USB drive and learn about Windows shortcut files and how malicious actors are using .lnk files to spread malware.
 If you are here, you have probably heard about how to hire a hacker on the dark or deep web. Using regular web browsers, we can only have access to four percent of the net. The other 96% must be accessed through a unique browser, Tor.
If you are here, you have probably heard about how to hire a hacker on the dark or deep web. Using regular web browsers, we can only have access to four percent of the net. The other 96% must be accessed through a unique browser, Tor.
 With the rise in cybersecurity threats, having a strong, secure password has become more critical than ever. In fact, did you know that the key reason behind 80% of data breaches in 2019 was password compromise?
With the rise in cybersecurity threats, having a strong, secure password has become more critical than ever. In fact, did you know that the key reason behind 80% of data breaches in 2019 was password compromise?
 Blockchain technology has spawned not only a new industry but also a set of subcultures within the cryptocurrency space. While these cultures have certain attributes in common, each group has its own individual characteristics that differentiate them from one another. This article is an anthropological overview by an author with absolutely no knowledge of anthropology. It may serve as a guide to those like herself who may inadvertently find themselves engulfed in a foreign culture, having mistaken one group for the other.
Blockchain technology has spawned not only a new industry but also a set of subcultures within the cryptocurrency space. While these cultures have certain attributes in common, each group has its own individual characteristics that differentiate them from one another. This article is an anthropological overview by an author with absolutely no knowledge of anthropology. It may serve as a guide to those like herself who may inadvertently find themselves engulfed in a foreign culture, having mistaken one group for the other.
 In addition to sharing personal data of essential people in Indonesia, Bjorka also studied death cases such as Munir and Brigadier J. Who was Bjorka?
In addition to sharing personal data of essential people in Indonesia, Bjorka also studied death cases such as Munir and Brigadier J. Who was Bjorka?
 A look at some of the hardware tools that hackers use to access and corrupt your computer.
A look at some of the hardware tools that hackers use to access and corrupt your computer.
 In an increasingly digitized world, cybercriminals are taking to the internet to share exactly how they commit fraud.
In an increasingly digitized world, cybercriminals are taking to the internet to share exactly how they commit fraud.
 Nowadays, Cyber security is a trending topic around the globe. It has become a necessity for every business with the growing cyber threats.
Nowadays, Cyber security is a trending topic around the globe. It has become a necessity for every business with the growing cyber threats.
 A digital forensics by CYE's Critical Cyber Operations group found that the the "Outlaw Hacking Group" may be back.
A digital forensics by CYE's Critical Cyber Operations group found that the the "Outlaw Hacking Group" may be back.
 How to become an ethical hacker
How to become an ethical hacker
 Spyier, keylogging, and hacking using cookies are some of the most common ways Facebook Messenger accounts get hacked.
Spyier, keylogging, and hacking using cookies are some of the most common ways Facebook Messenger accounts get hacked.
 The virtual world is going to be where we LIVE. How will this change the economic dynamics, gravity, and equilibrium in the physical world? In search of the answers, I shaped these predictions for investing and living.
The virtual world is going to be where we LIVE. How will this change the economic dynamics, gravity, and equilibrium in the physical world? In search of the answers, I shaped these predictions for investing and living.
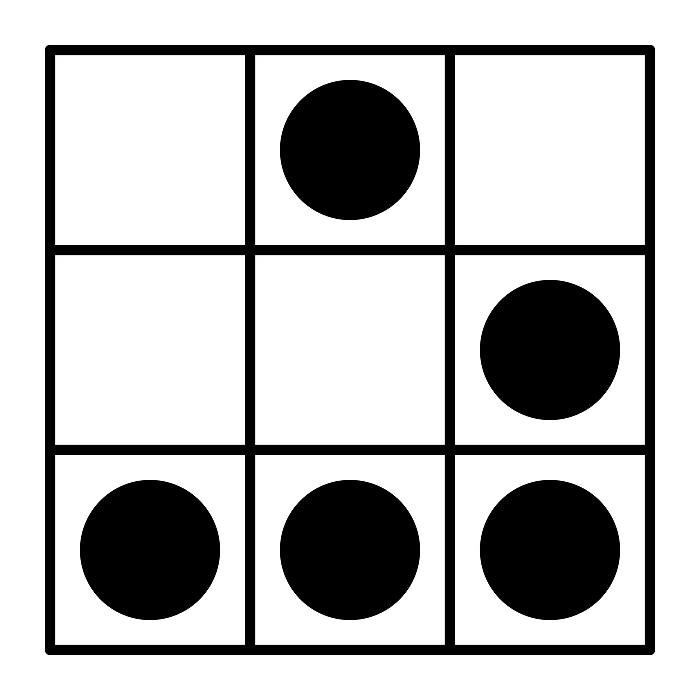
 How a $20 Raspberry Pi can be used as pentest tool and what to look out for to protect your network.
How a $20 Raspberry Pi can be used as pentest tool and what to look out for to protect your network.
 Common misconceptions about hacking that makes you vulnerable and how to avoid them.
Common misconceptions about hacking that makes you vulnerable and how to avoid them.
 Understanding Robots.txt, Favicon, Sitemap.xml, HTML Headers and the Framework stack
Understanding Robots.txt, Favicon, Sitemap.xml, HTML Headers and the Framework stack
 He was ahead his time in 2009, but today there are other threat actors in action. Here's how he seems to have gotten away with stealing millions of dollars.
He was ahead his time in 2009, but today there are other threat actors in action. Here's how he seems to have gotten away with stealing millions of dollars.
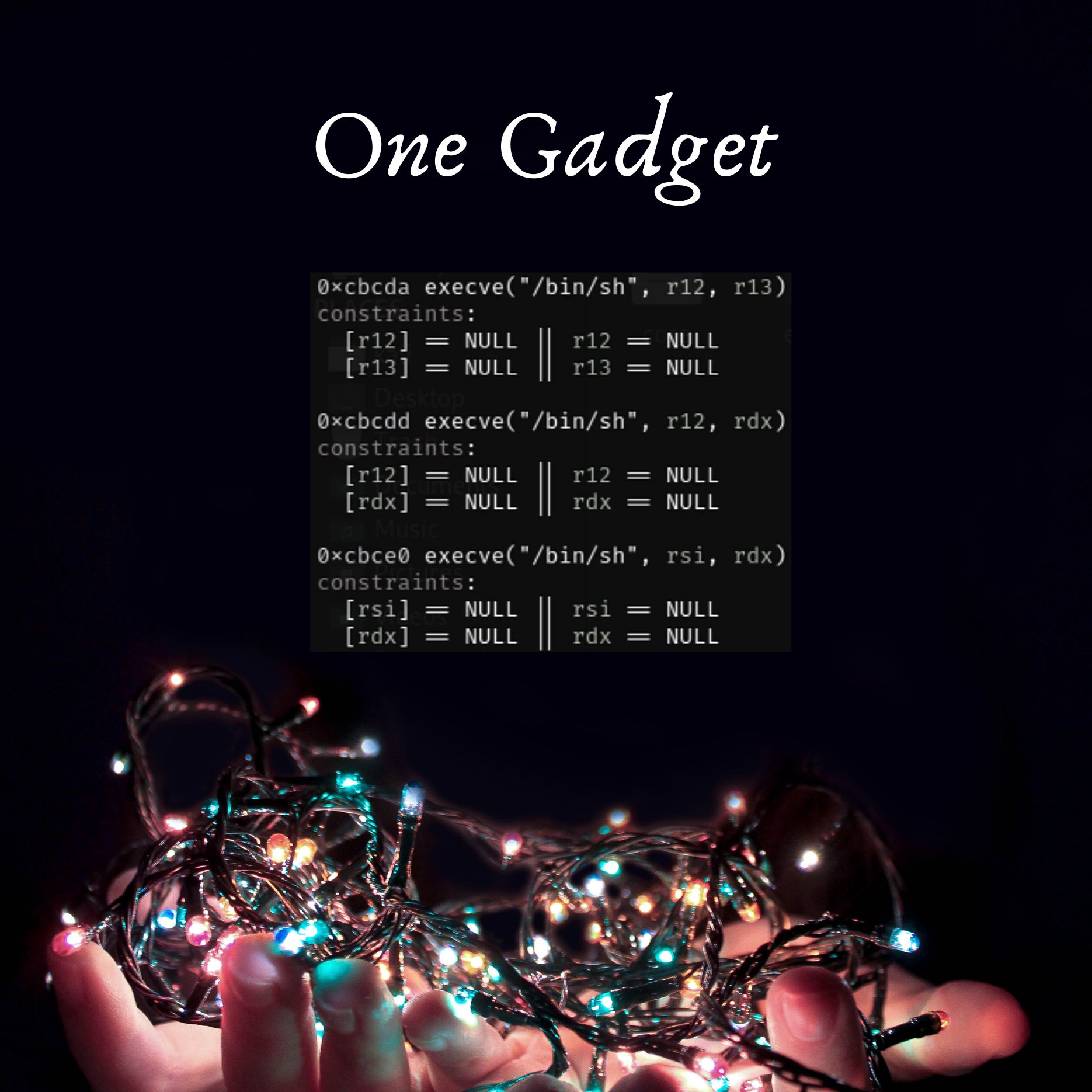
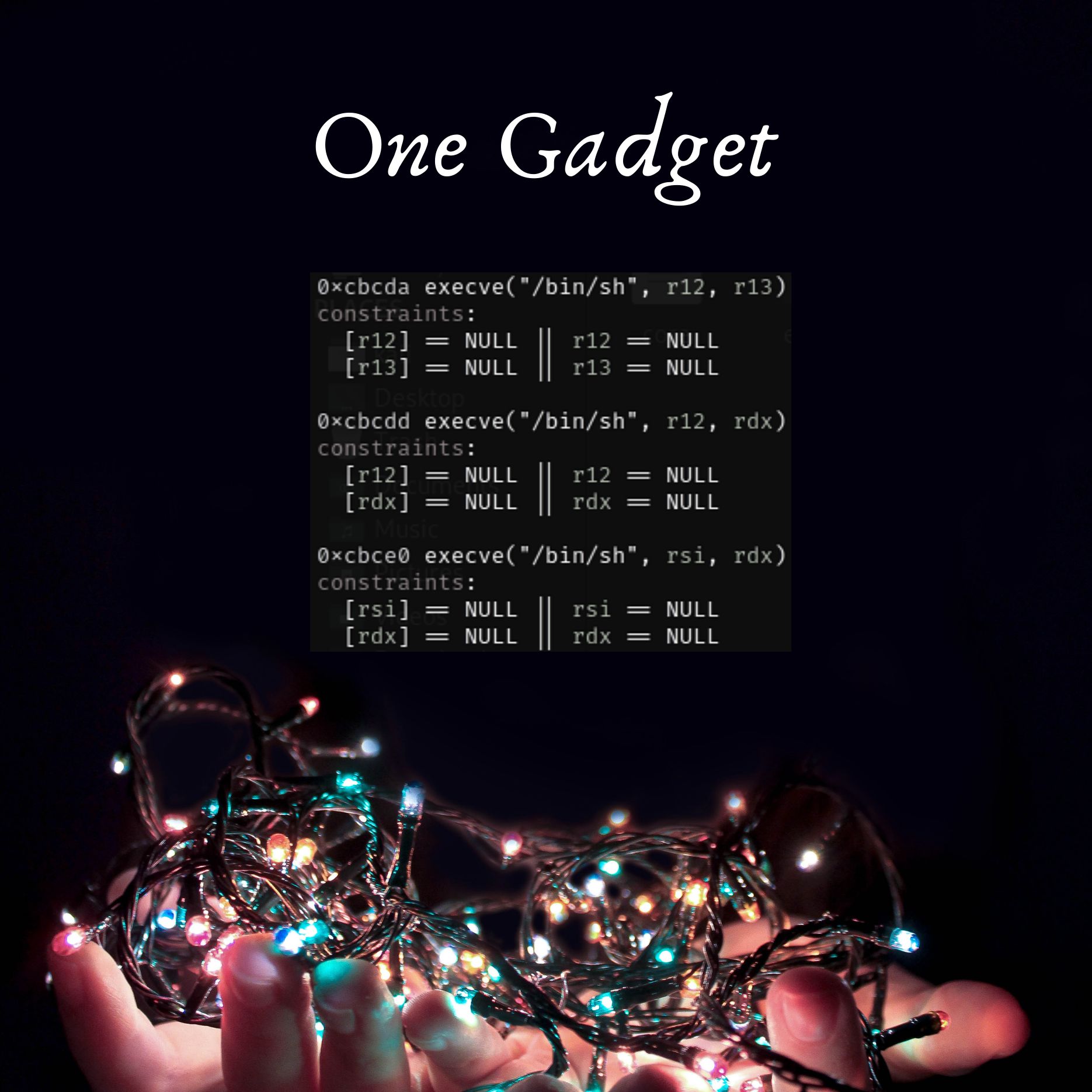 This post uses a concrete CTF problem to show you step-by-step how to find and execute a one gadget and eventually spawn a shell.
This post uses a concrete CTF problem to show you step-by-step how to find and execute a one gadget and eventually spawn a shell.
 Know How AI-based cybersecurity tools can provide up to date knowledge of global and industry specific threats to help make critical prioritization decisions
Know How AI-based cybersecurity tools can provide up to date knowledge of global and industry specific threats to help make critical prioritization decisions
 Self care through physical exercise can help hackers with stress and energy.
Self care through physical exercise can help hackers with stress and energy.
 Did you ever wonder how a hacker can compromise a system? This Behind the Scenes (BTS) walkthrough takes us through a possible scenario using a known exploit.
Did you ever wonder how a hacker can compromise a system? This Behind the Scenes (BTS) walkthrough takes us through a possible scenario using a known exploit.
 Hackers are also ordinary people who fear, worry, and feel ashamed of their atrocities
Hackers are also ordinary people who fear, worry, and feel ashamed of their atrocities
 Instances of cyberattacks, especially those targeting WordPress websites, are on the rise across the internet. The most recent attack to hit WordPress users affected some 700,000 sites running a vulnerable plugin.
Instances of cyberattacks, especially those targeting WordPress websites, are on the rise across the internet. The most recent attack to hit WordPress users affected some 700,000 sites running a vulnerable plugin.
 I believe strongly if we get answers to these questions from a source with gravitas, such as Sabu, we will understand how to navigate the future.
I believe strongly if we get answers to these questions from a source with gravitas, such as Sabu, we will understand how to navigate the future.
 The Way of the CybeRonin
The Way of the CybeRonin
 The takeover of high profile Twitter profiles last month on July 15 made headlines when public figures like former President Barack Obama, Jeff Bezos, and Elon Musk began announcing that they wanted to “give back” to the community.
The takeover of high profile Twitter profiles last month on July 15 made headlines when public figures like former President Barack Obama, Jeff Bezos, and Elon Musk began announcing that they wanted to “give back” to the community.
 Hacker and doubt
Hacker and doubt
 In this article, I discuss how you can convert one android phone into a fully working Kali Linux hacking machine.
In this article, I discuss how you can convert one android phone into a fully working Kali Linux hacking machine.
 The horizontal rule
The horizontal rule
is simply a horizontal line used to signal a change in topic or a thematic break in a section of an HTML page. If you have ever tinkered with it, you may have been content with its default settings. However, many developers run into a couple of issues when trying to customize it to suit their design needs.
 What is a Growth hacker mindset and its 14 habits?
What is a Growth hacker mindset and its 14 habits?
 In this post, I’m going to share concepts, methods, and tools used by researchers both for finding secrets and exploiting them. I’ll also list mitigation ideas.
In this post, I’m going to share concepts, methods, and tools used by researchers both for finding secrets and exploiting them. I’ll also list mitigation ideas.
 Around age seven, two years after the divorce and relocation from Queens, Richard took up the hobby of launching model rockets in nearby Riverside Drive Park
Around age seven, two years after the divorce and relocation from Queens, Richard took up the hobby of launching model rockets in nearby Riverside Drive Park
 Server-side request forgery (SSRF) vulnerabilities can lead to total system compromise. Discover where they’re common, examples, and prevention tips.
Server-side request forgery (SSRF) vulnerabilities can lead to total system compromise. Discover where they’re common, examples, and prevention tips.
 Numerous signs scattered throughout the first floor preach the dangers of unsecured doors and propped-open fire exits.
Numerous signs scattered throughout the first floor preach the dangers of unsecured doors and propped-open fire exits.
 The horizontal rule
The horizontal rule
is simply a horizontal line used to signal a change in topic or a thematic break in a section of an HTML page. If you have ever tinkered with it, you may have been content with its default settings. However, many developers run into a couple of issues when trying to customize it to suit their design needs.