fix(deps): update dependency phpoffice/phpspreadsheet to v1.29.9 [security] #814
Add this suggestion to a batch that can be applied as a single commit.
This suggestion is invalid because no changes were made to the code.
Suggestions cannot be applied while the pull request is closed.
Suggestions cannot be applied while viewing a subset of changes.
Only one suggestion per line can be applied in a batch.
Add this suggestion to a batch that can be applied as a single commit.
Applying suggestions on deleted lines is not supported.
You must change the existing code in this line in order to create a valid suggestion.
Outdated suggestions cannot be applied.
This suggestion has been applied or marked resolved.
Suggestions cannot be applied from pending reviews.
Suggestions cannot be applied on multi-line comments.
Suggestions cannot be applied while the pull request is queued to merge.
Suggestion cannot be applied right now. Please check back later.
This PR contains the following updates:
1.29.8->1.29.9GitHub Vulnerability Alerts
CVE-2025-22131
Summary
The researcher discovered zero-day vulnerability Cross-Site Scripting (XSS) vulnerability in the code which translates the XLSX file into a HTML representation and displays it in the response.
Details
When generating the HTML from an xlsx file containing multiple sheets, a navigation menu is created. This menu includes the sheet names, which are not sanitized. As a result, an attacker can exploit this vulnerability to execute JavaScript code.
PoC
Create an XLSX file with multiple sheets :
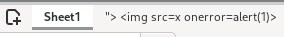
Generate the HTML content
Impact
XSS can cause a variety of problems for the end user that range in severity from an annoyance to complete account compromise.
Example of impacts :
CVE-2025-23210
Product: PhpSpreadsheet
Version: 3.8.0
CWE-ID: CWE-79: Improper Neutralization of Input During Web Page Generation ('Cross-site Scripting')
CVSS vector v.3.1: 5.4 (AV:N/AC:L/PR:L/UI:R/S:C/C:L/I:L/A:N)
CVSS vector v.4.0: 4.8 (AV:N/AC:L/AT:N/PR:L/UI:A/VC:L/VI:L/VA:N/SC:L/SI:L/SA:N)
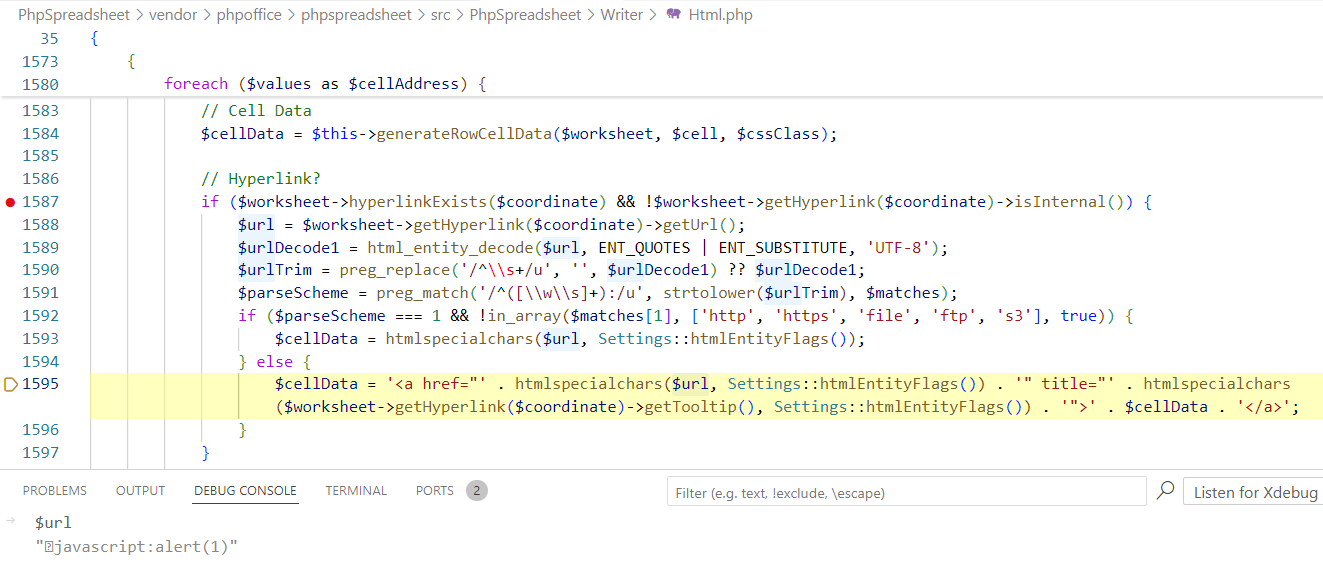
Description: an attacker can use special characters, so that the library processes the javascript protocol with special characters and generates an HTML link
Impact: executing arbitrary JavaScript code in the browser
Vulnerable component: class
PhpOffice\PhpSpreadsheet\Writer\Html, methodgenerateRowExploitation conditions: a user viewing a specially generated xml file
Mitigation: additional sanitization of special characters in a string
Researcher: Igor Sak-Sakovskiy (Positive Technologies)
Research
The researcher discovered zero-day vulnerability Bypass XSS sanitizer using the javascript protocol and special characters in Phpspreadsheet.
The following code is written on the server, which translates the XML file into an HTML representation and displays it in the response.
Listing 4. Source code on the server
The contents of the xml file -
./doc/file.xmlListing 5. The contents of the xml file
Due to the load with a special character in front of the javascript protocol, the execution flow hits line 1595, not 1593.
Figure 4. Generating a link bypassing a regular expression
In the response from the server, you can see which special character is located in front of the javascript protocol after conversion.
Figure 5. Response from the server with a special character
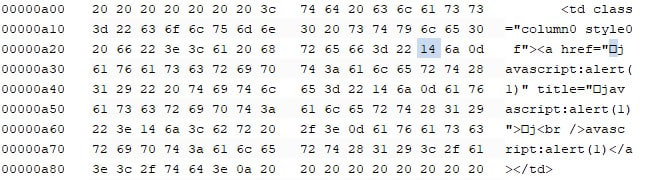
When viewing the rendered result, a link becomes visible in the browser, and when clicked, the embedded JavaScript code will be executed.
Figure 6. Executing JavaScript code

Credit
Igor Sak-Sakovskiy (Positive Technologies)
Release Notes
PHPOffice/PhpSpreadsheet (phpoffice/phpspreadsheet)
v1.29.9Compare Source
Fixed
Configuration
📅 Schedule: Branch creation - "" (UTC), Automerge - At any time (no schedule defined).
🚦 Automerge: Disabled by config. Please merge this manually once you are satisfied.
♻ Rebasing: Whenever PR becomes conflicted, or you tick the rebase/retry checkbox.
🔕 Ignore: Close this PR and you won't be reminded about this update again.
This PR was generated by Mend Renovate. View the repository job log.